Presigned Post Aws S3 Curl Upload File
How to Properly Use AWS S3 Presigned URLs
Upload a file using Lambda with Python and Chalice
Last week, my boyfriend developers @kiziltepecinar, @ege.gurkan2608, and I were struggling to integrate AWS S3 Presigned URL file uploads to our website.
We know at that place are many tutorials on the topic, including AWS's own documentation, only all of the ones that we looked at were onetime or missing some important points, and then we decided to write a consummate tutorial. If you're a programmer who wants to upload files to S3 using presigned URLs, then you're in the right place.
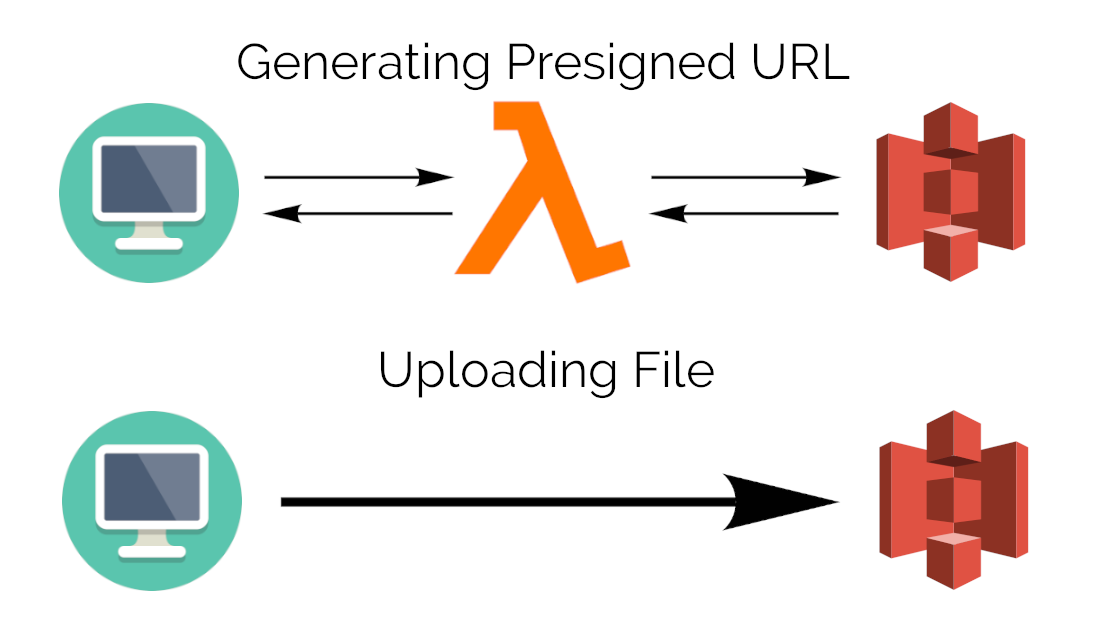
In this tutorial, nosotros'll deploy a Remainder API to Lambda using Beaker, call the Residuum API to become a presigned URL, and finally upload a file directly to the S3 bucket.
Getting Started With Chalice
"AWS Beaker is a Python Serverless Microframework for AWS and allows you to quickly create and deploy applications that use Amazon API Gateway and AWS Lambda." — Alex Pulver, AWS Programmer Blog
If you want to become started on your own, you can follow the Chalice documentation and jump to the Configuring AWS section.
First of all, you need to configure your AWS keys on your estimator then Chalice tin can access Lambda. (More data tin can be found here.)
$ mkdir ~/.aws
$ true cat >> ~/.aws/config
[default]
aws_access_key_id=YOUR_ACCESS_KEY_HERE
aws_secret_access_key=YOUR_SECRET_ACCESS_KEY
region=YOUR_REGION (such as us-west-two, u.s.-west-ane, etc) Afterwards it'southward configured, let'south start our Beaker project by running the commands below.
$ pip install chalice
$ chalice new-project s3_presigned_file_upload This will create 2 files: app.py and requirements.txt, found under s3_presigned_file_upload. When we open app.py with our favorite editor, we'll face the code below (and some comments):
Now we demand to configure the S3 bucket and Lambda permissions to let our Lambda function create presigned URLs successfully.
Configuring AWS
First, we need to create an S3 Saucepan. (If you already have 1, you can go with it, but remember to do the configurations below.)
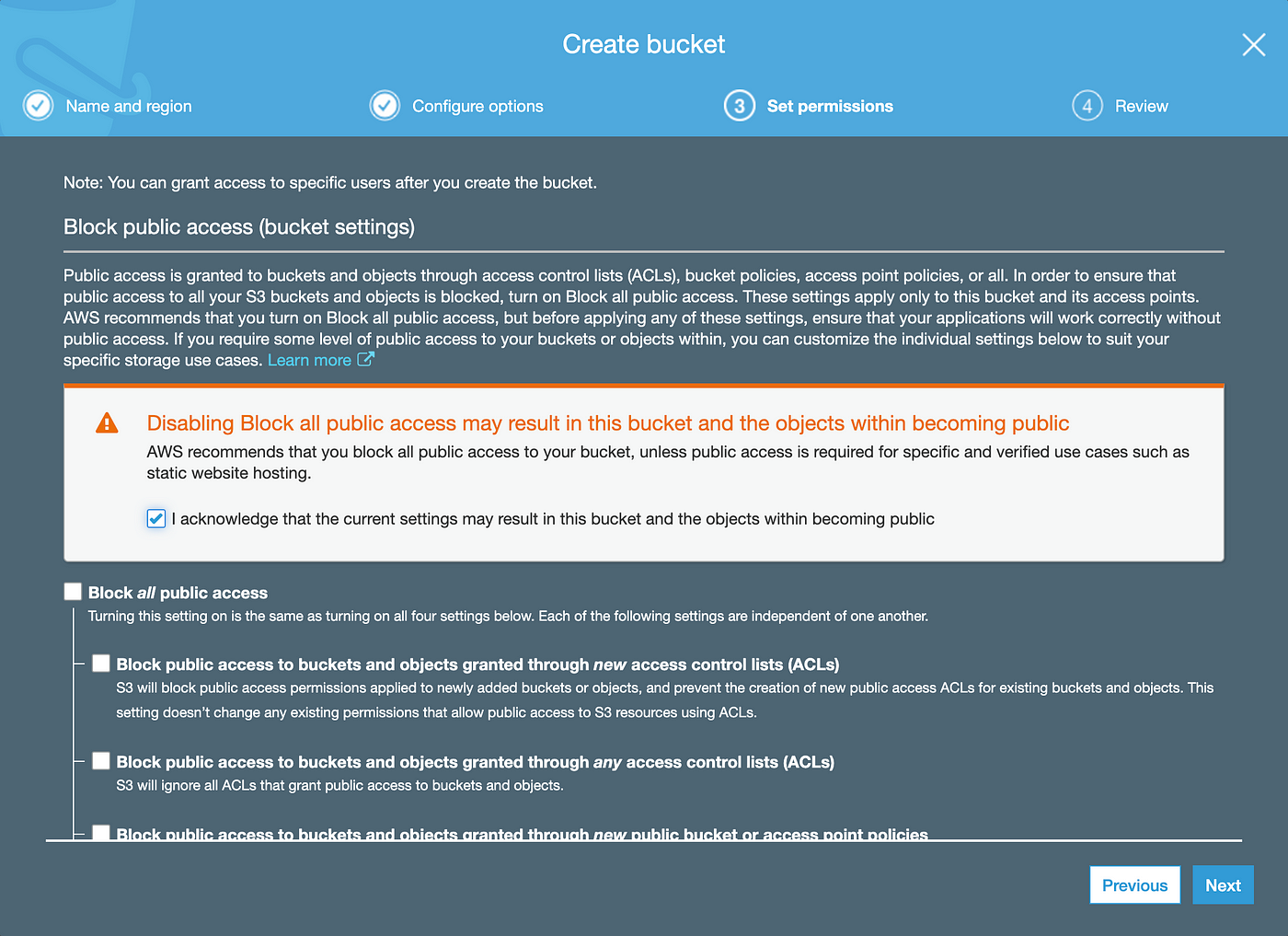
Log in to the panel, navigate to S3, and click on the bluish "Create bucket" button. We'll proper noun our bucket presigned-url-upload and keep everything every bit default except "Block all public access" under Ready Permissions. (You need to plough it off if y'all desire to give the public admission to some files, such as contour photos.)
Subsequently creating the bucket, we also need to edit the CORS configuration of the bucket. Navigate into the bucket, choose "CORS Configuration" under the Permissions tab, and copy the configuration below:
Next, nosotros need to give Lambda the necessary permissions.
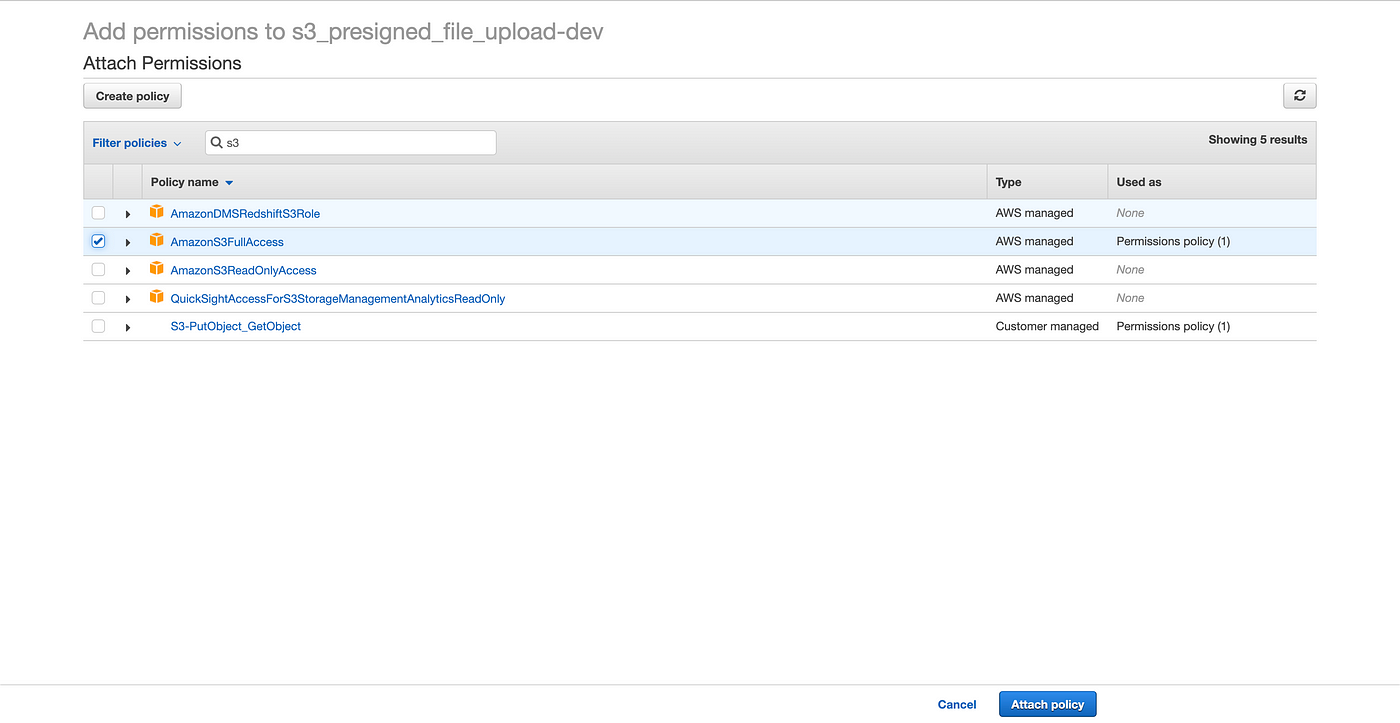
To practise this, navigate to the Lambda dashboard, select your function (s3_presigned_file_upload-dev, in my situation), become to the Permissions tab, and click on the Part proper name (same as your function proper name).
This will open an IAM dashboard. Click on "Attach Policies," search for "S3," select "AmazonS3FullAccess," and click on "Attach Polices" on the bottom left; this gives Lambda the necessary permissions to access S3 and generate the URL [two].
Generating a Presigned URL
We'll utilize boto3 to connect to our S3 Saucepan and generate the URL; therefore, we need to change our Lambda lawmaking as shown beneath [3]:
What this code does is later on it receives a GET request at /generate_presigned_url with a file_name in the parameters, information technology'll send usa a presigned URL, which will enable the states to put a file to S3 using a PUT request.
Remember, in this instance, BUCKET_NAME is presigned-url-upload, and I'grand working in the us-due east-two region. After irresolute the lawmaking, nosotros need to deploy it to Lambda using Chalice [1].
$ beaker deploy This should produce an output similar to the 1 below:
Creating deployment packet.
Creating IAM office: s3_presigned_file_upload-dev
Creating lambda part: s3_presigned_file_upload-dev
Creating Rest API
Resources deployed:
- Lambda ARN: arn:aws:lambda:us-e-2:543915562838:office:s3_presigned_file_upload-dev
- Rest API URL: https://f93b1rbf23.execute-api.us-due east-ii.amazonaws.com/api/ It'southward of import to take notation of the Rest API URL (https://f93b1rbf23.execute-api.u.s.-east-2.amazonaws.com/api/).
Now our API is deployed, and it's time to test.
Uploading the File
You can send your requests however you lot want, merely for testing purposes, I discover Postman really useful. In order to test, nosotros'll send the photo below to our S3 bucket. (It's a random imitation man photograph from This Person Does Non Exist.)

First, we demand to send a Go request to our Lambda and get our presigned URL. In this case, nosotros'll be naming our file test.jpg.
https://f93b1rbf23.execute-api.us-e-two.amazonaws.com/api/generate_presigned_url?file_name=exam.jpg 
The long URL with all those parameters is our presigned URL, on which we'll be performing our 2d request, over again using Postman. Create a new request, and copy the URL, remembering to fix the request type to PUT.
We also need to set a header with the primal 10-amz-acl and the value public-read under the Headers tab. In add-on, under the Body tab, select the binary type, and add together your file [four].

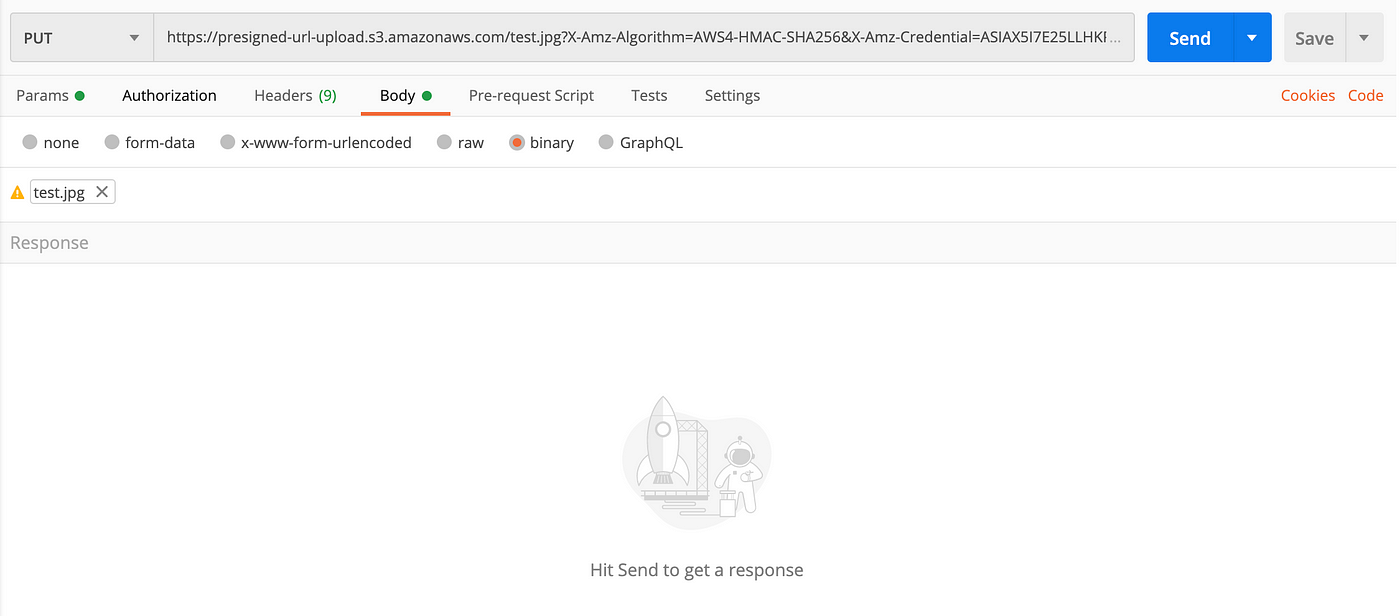
After pressing Send, getting 200 OK status means everything is configured correctly and the file can be accessed from:
https://<BUCKET_NAME>.s3.amazonaws.com/<FILE_NAME> If y'all desire to upload a file from a website or a mobile awarding, all you lot need to do is to call the above PUT request with the same configuration.
Thank you very much for reading until the end. If you face whatsoever problems, delight feel free to write a response explaining your situation, and I'll try to help as much as I tin.
Notes
[1] The public-read access control list (ACL) enables the file to be read publicly after the upload. You can read more nigh it here.
[2] Both setting the CORS configuration to take requests from all origins and giving Lambda full access over S3 aren't platonic security-wise, and there are amend approaches. Go along that in mind.
[3] Although it may seem counterintuitive, there's no need to put boto3 in requirements.txt.
[4] In many resources I've encountered, it was written that "if file proper noun and extension doesn't lucifer exactly (with the i in the presigned URL), it'll generate a SignatureDoesNotMatch error." However, it wasn't true — I fifty-fifty managed to upload the same examination.jpg to a presigned URL for file_name_and_format_wrong.png. If you face a SignatureDoesNotMatch error, check your headers; non putting the ten-amz-acl header causes the fault.
Source: https://betterprogramming.pub/how-to-properly-use-aws-s3-presigned-urls-147a449227f9
0 Response to "Presigned Post Aws S3 Curl Upload File"
إرسال تعليق